.jpg)
Microsoft's Defender ATP Research Team today issued guidance on how to defend against attacks targeting Exchange servers by blocking malicious activity identified with the help of behavior-based detection.
The Microsoft researchers based their analysis on multiple campaigns of Exchange attacks investigated during early April which showed how the malicious actors deploying web shells on on-premises Exchange servers.
Multiple fileless techniques were also used as part of these attacks, "adding another layer of complexity to detecting and resolving these threats, and demonstrating how behavior-based detections are key to protecting organizations."
Exploits increasingly used in Exchange attacks
While threat actors commonly use social engineering and drive-by downloads to steal organization employees' credentials to move through the network and, eventually, to get control of an Exchange server, Microsoft says that the attacks are also increasingly focused on exploiting unpatched Exchange servers.
When attempting to exploit Exchange vulnerabilities, "attackers exploit a remote code execution vulnerability affecting the underlying Internet Information Service (IIS) component of a target Exchange server," Microsoft explained.
"This is an attacker’s dream: directly landing on a server and, if the server has misconfigured access levels, gain system privileges."
"The first scenario is more common, but we’re seeing a rise in attacks of the second variety," the Microsoft Defender ATP Research Team added.
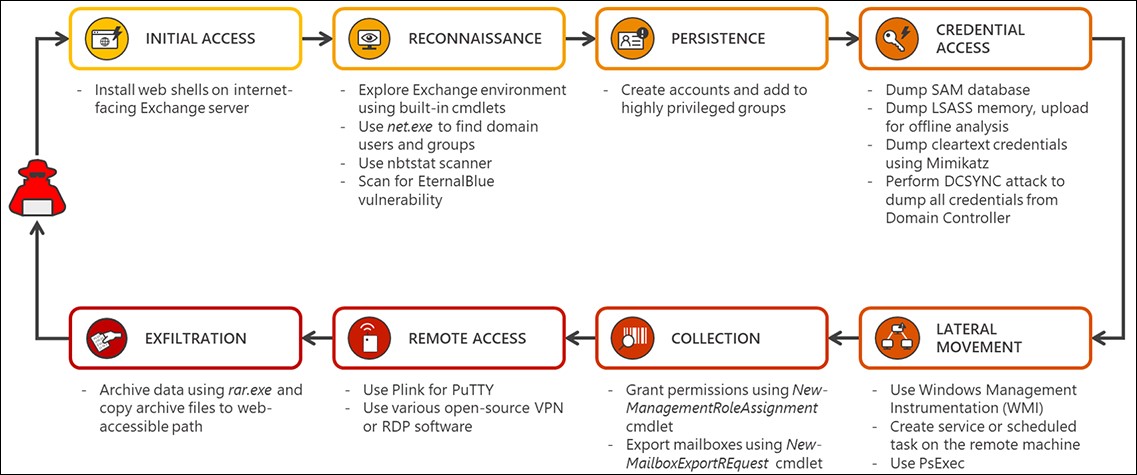
"In many cases, after attackers gain access to an Exchange server, what follows is the deployment of web shell into one of the many web-accessible paths on the server," Microsoft further explained.
Web shells are tools hackers deploy on compromised servers to gain and maintain access, as well as to remotely execute arbitrary commands and code, to deliver malware payloads, and to move laterally to other devices within the network.
They can be uploaded in a wide variety of forms, from programs designed to provide web shell features and Perl, Python, Ruby, and Unix shell scripts to app plugins and PHP or ASP code snippets injected within web apps.
The U.S. National Security Agency (NSA) and the Australian Signals Directorate (ASD) issued a joint report in April, warning of malicious actors increasing their attacks on vulnerable web servers to deploy web shell backdoors.
CVE-2020-0688 specifically targeted with exploits
Microsoft's researchers also said that following their investigation of recent Exchange attacks they saw a rise in attacks exploiting Exchange vulnerabilities, "specifically, attacks that exploit Exchange vulnerabilities like CVE-2020-0688."
"The security update that fixes this vulnerability has been available for several months, but, notably, to this day, attackers find vulnerable servers to target."
This flaw is present in the Exchange Control Panel (ECP) component and it is caused by Exchange's failure to create unique cryptographic keys when being installed.
Once successfully exploited, CVE-2020-0688 enables authenticated attackers to execute code remotely with SYSTEM privileges on exploited servers and fully compromise it.
Hackers were already scanning for vulnerable Microsoft Exchange servers two weeks after Redmond addressed the CVE-2020-0688 vulnerability.
Your regular reminder to patch Exchange vulnerability CVE-2020-0688, and also migrate off Exchange 2007 (as it is also vulnerable and has no patch) and migrate off Exchange 2010 (goes EOL in 4 months).
This vulnerability is actively used in attacks.
— Kevin Beaumont (@GossiTheDog) June 19, 2020
In April, 82.5% of all found Exchange servers unpatched against were not yet patched, with Microsoft previously warning that it could be used in ransomware attacks, and NSA listing it as one of the security flaws used to deploy backdoors on vulnerable servers.
NSA also warned about the same remote code execution flaw one month earlier, reminding users to patch their servers if they want to block attackers from executing commands on Microsoft Exchange servers using email credentials.
State-backed hacking groups were also observed by security researchers brute-forcing credentials by leveraging Exchange Web Services (EWS) to exploit the CVE-2020-0688 flaw, attacks that were also confirmed by a U.S. Department of Defense (DoD) source.
Since Exchange servers are high-value objectives in enterprise environments targeted using evasive, fileless techniques, they should be at the top of the list of most important assets to protect.
Microsoft advises customers to always apply the latest Exchange servers, keep their antimalware solutions enabled at all times, make sure that sensitive groups and roles are frequently reviewed for suspicious removals and additions, restrict access by applying the principle of least privilege, and immediately investigate suspicious activity alerts.
"exchange" - Google News
June 25, 2020 at 01:25AM
https://ift.tt/2Vexb6q
Microsoft: Attackers increasingly exploit Exchange servers - BleepingComputer
"exchange" - Google News
https://ift.tt/3c55nbe
https://ift.tt/3b2gZKy
Exchange
Bagikan Berita Ini















0 Response to "Microsoft: Attackers increasingly exploit Exchange servers - BleepingComputer"
Post a Comment